This short post will teach you what ransomware is and how to protect yourself. Indeed in recent times users, both at home and at work, are often rece
Read MoreOla the taxi aggregator based in India has been trying out everything to keep its competitor Uber far behind the company. The Indian Online taxi Aggre
Read MorePeople can look for ways to develop an optimal essay paragraph structure. An essay can be a written explanation of their thoughts regarding a specific
Read MoreHaving already established that your eCommerce checkout is the most vulnerable part of the whole shopping experience, you’ve probably done everything
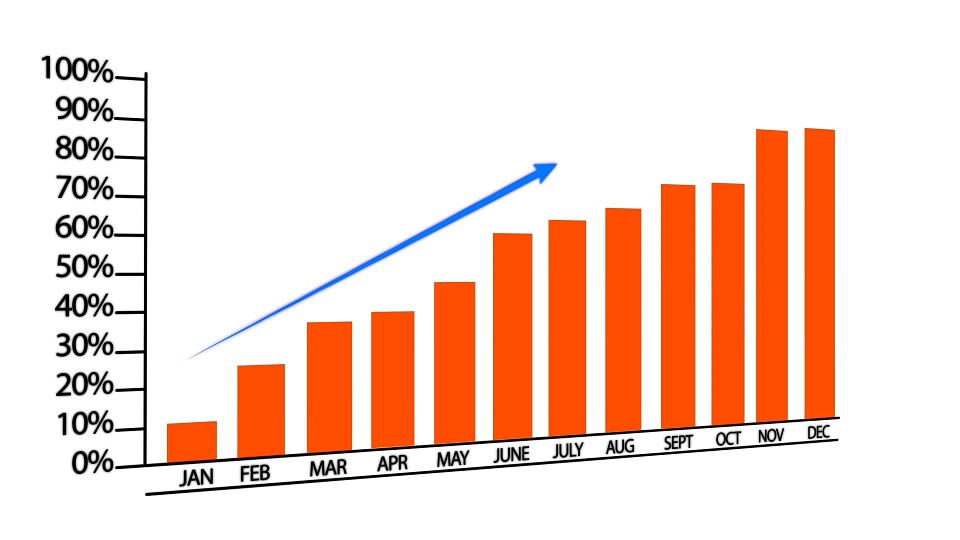
Read MoreBy now you must be aware that affiliate marketing is all about making angles. It is about creating a dance choreography that brings together merchants
Read MoreWe all know Kali Linux is Most Advanced Penetration Testing Distribution, Ever made. Most of the ethical hackers use Kali Linux for pen-testing.Usuall
Read MoreA Ph.D. student might experience writer’s block and look for ways to overcome it. Doctoral students complete their dissertation as a way of presenting
Read MorePenBox – A Penetration Testing Framework A Penetration Testing Framework , The Hacker’s Repo our hope is in the last version we will have every scrip
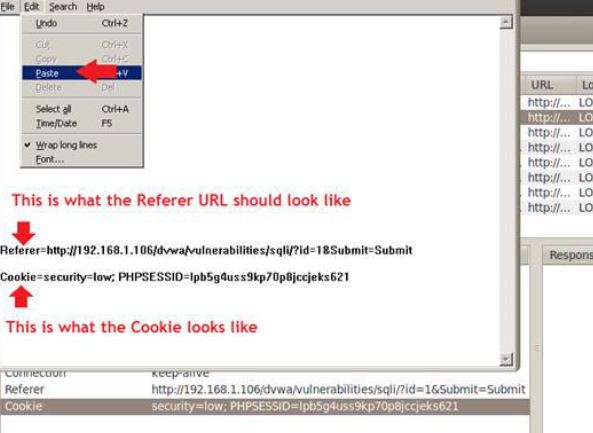
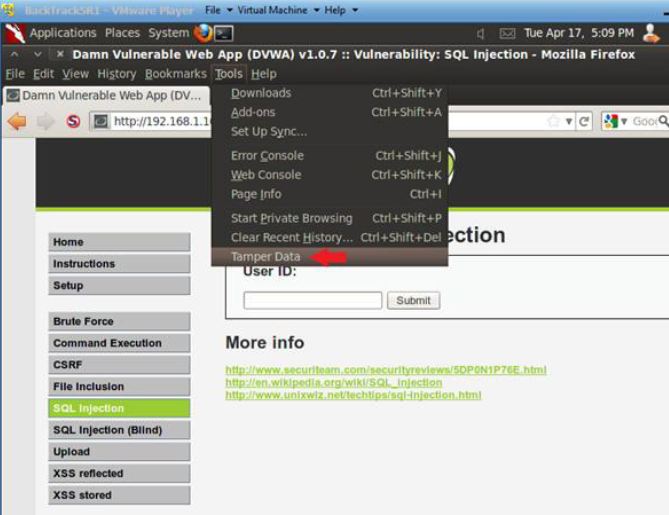
Read MoreWelcome Gurkhas, in Part 3 . . . Section 9: Obtain PHP Cookie 1. SQL Injection Menu o Instructions: 1. Select “SQL Injection” from the left naviga
Read MoreLet’s start part 2. Open Console Terminal and Retrieve IP Address open a console terminal Instructions: 1. Click on the console terminal
Read More