Most people now realize how important it is to stay safe online in the tech age. Both businesses and individuals can be caught out by online cybercr
Read MoreHistoric hacks are making headlines practically every month these days. Some breaches wind up with a hacker arrested, but often the perpet
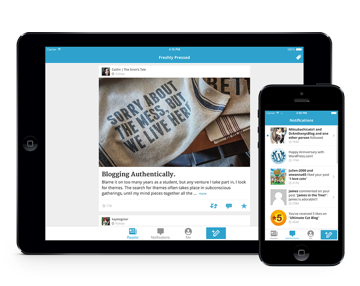
Read MoreMillions of people across the globe have a blog right now, for either personal or business use. If you’re someone who is in this boat and spends man
Read MorePhishing is a fraudulent attempt at stealing sensitive and confidential data of a user through the means of email. With an increase in the number of i
Read MoreRansomware attack is one of the major cyber-attacks that is employed by attackers through the means of a malicious software. The primary purpose of su
Read MoreYour Windows PC stores tons of useful and sensitive data that could be under security threat due to various reasons. The data you store on your Window
Read MoreAccording to Cyber Security Ventures, a business falls victim to a ransomware attack every 14 seconds. If you don’t want to form part of those stati
Read MoreIf you have chosen to use the open source resources, then you are automatically signing up for a potential security threat to your digital property.
Read MoreThere seems to be no end to cybersecurity threats. You can come up with several methods and procedures to prevent the breach of security and y
Read MoreTwo years ago, we published an article of the top 5 ethical and unethical hacker forums on the internet. Time has passed since, and most of them don
Read More